This guide explains how to integrate external systems with Tracer, including the payload requirements, integration flow, and best practices for achieving optimal performance.Documentation Index
Fetch the complete documentation index at: https://docs.lerian.studio/llms.txt
Use this file to discover all available pages before exploring further.
Integration overview
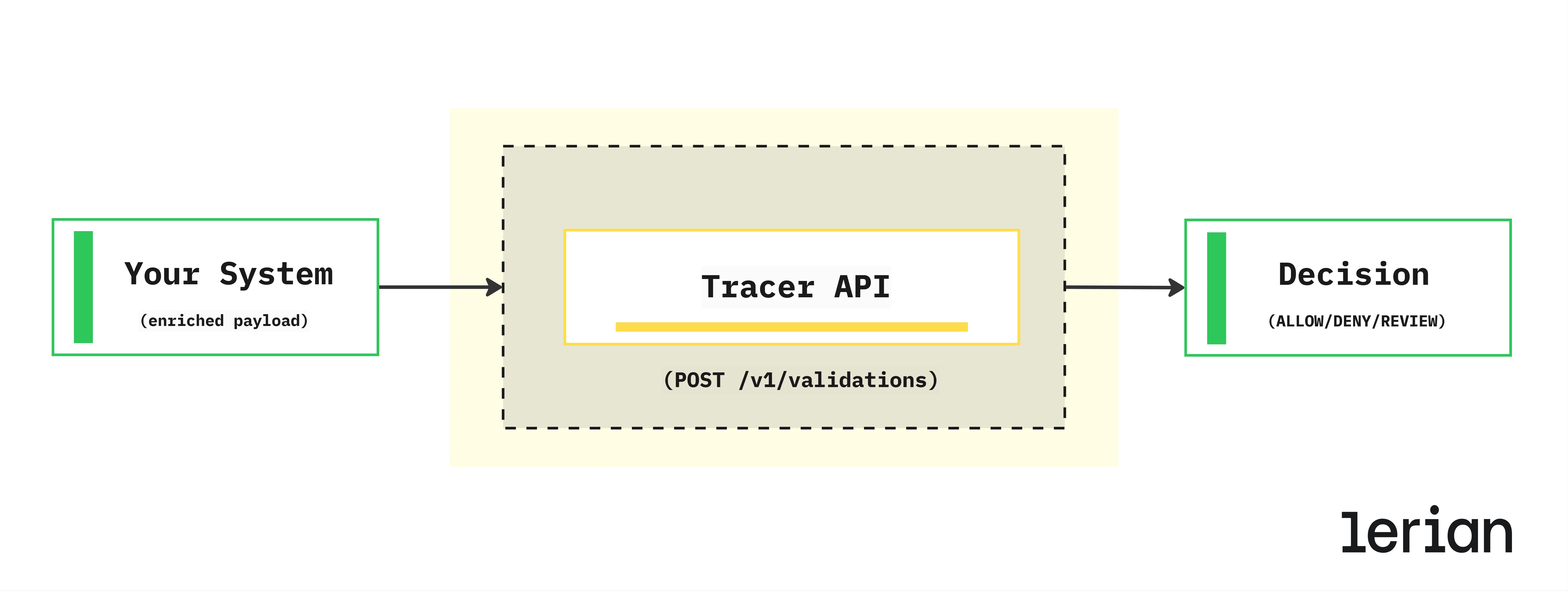
Tracer is designed to be called by authorization systems (payment gateways, workflow orchestrators, or transaction processors) that need real-time validation decisions. The integration follows a simple request-response pattern:
Payload-Complete Pattern
Tracer uses the Payload-Complete Pattern, which means all context required for validation must be included in the request. This design ensures:
| Benefit | Description |
|---|---|
| Predictable latency | No external calls during validation; response time stays under 80ms |
| Simplicity | Single request contains everything needed for decision |
| Reliability | No dependency on external services during validation |
| Flexibility | Your system controls data freshness and enrichment logic |
Your responsibilities
As the integrating system, you are responsible for:- Enriching the payload with account, segment, portfolio, and merchant data before calling Tracer
- Providing accurate context for rule and limit evaluation—Tracer cannot fetch missing data
- Handling the decision (ALLOW, DENY, or REVIEW) appropriately in your workflow
- Implementing retry logic if Tracer is temporarily unavailable
- Managing review workflows when Tracer returns
REVIEW—Tracer does not include case management
Tracer’s responsibilities
Tracer is responsible for:- Evaluating rules against the provided context
- Checking limits against current usage
- Recording audit trail for compliance
- Returning decision with detailed information
Integration flow
Follow these steps to integrate your system with Tracer.
Step 1: Prepare the transaction context
Before calling Tracer, gather all relevant data from your systems: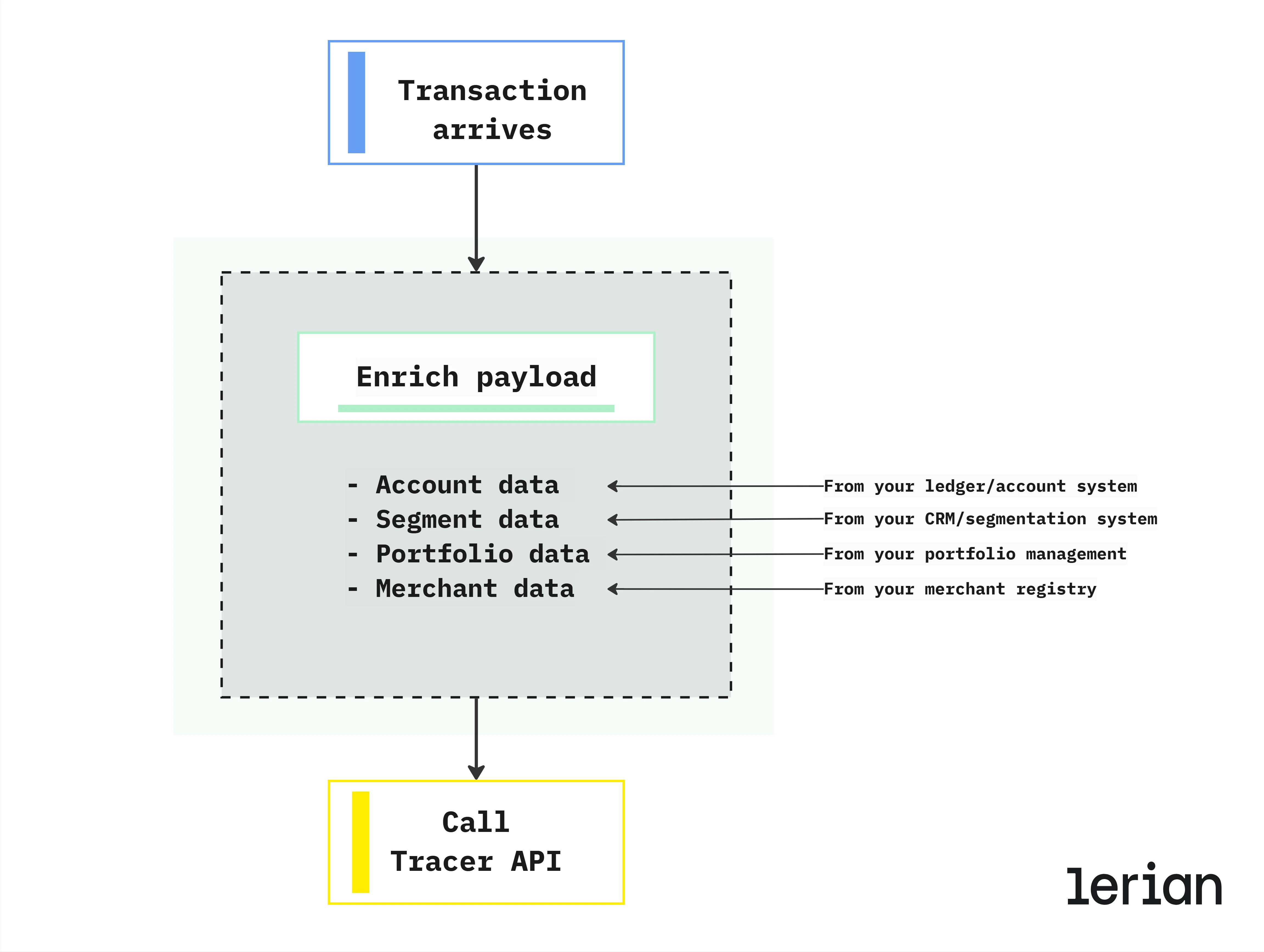
Step 2: Call Tracer API
Send a POST request to/v1/validations with the complete transaction context including:
- Transaction details (type, subType, amount, currency, timestamp)
- Account information (required)
- Optional: segment, portfolio, merchant, and custom metadata
Step 3: Handle the response
Process the decision returned by Tracer:| Decision | Action |
|---|---|
ALLOW | Proceed with the transaction |
DENY | Reject the transaction; show reason to user if appropriate |
REVIEW | Queue for manual review in your review system |
validationId for audit trail correlation, details about which rules matched, and current limit usage information.
Using metadata
Metadata allows you to pass custom fields that your rules can evaluate. Use this for context like channel, device information, customer tier, or any business-specific attributes.Metadata keys must be alphanumeric with underscores only, maximum 64 characters. Maximum 50 entries per request.
Performance considerations
Optimize your integration for low latency and high reliability.
Timeout budget
Tracer is designed to respond in under 80ms (p99). Configure your client timeout accordingly:| Configuration | Recommended value |
|---|---|
| Client timeout | 100ms |
| Connection timeout | 50ms |
| Read timeout | 100ms |
Retry strategy
Implement retry logic for transient failures:Fallback behavior
Decide what happens when Tracer is unavailable:| Strategy | When to use |
|---|---|
| Fail-open | Allow transaction if Tracer is down (prioritize availability) |
| Fail-closed | Deny transaction if Tracer is down (prioritize security) |
| Queue for review | Queue transaction for manual review |
Data freshness
Since you control the payload enrichment, data freshness is your responsibility. Tracer trusts the data you provide and cannot detect stale information.
| Data type | Freshness recommendation | Risk if stale |
|---|---|---|
| Account status | Real-time or near real-time | Transactions on suspended accounts may be allowed |
| Segment membership | Can be cached (changes infrequently) | Wrong limits or rules may apply |
| Portfolio assignment | Can be cached (changes infrequently) | Incorrect scope matching |
| Merchant data | Can be cached with periodic refresh | Risk rules may not trigger correctly |
Date and time format
All datetime fields must use RFC3339 format with mandatory timezone: Valid formats:
Integration checklist
Before going to production, verify:
- API Key is configured and secured
- Client timeout is set to 100ms
- Retry logic is implemented for 5xx errors
- Fallback behavior is defined
- All required fields are populated
- Timestamps use RFC3339 format with timezone
- Currency codes are uppercase ISO 4217
- Decision handling is implemented (ALLOW/DENY/REVIEW)
- Validation IDs are logged for audit trail correlation
Example integration (pseudocode)
Next steps
- Rules engine - Create rules that evaluate against the context you provide
- Spending limits - Configure limits that apply to your transaction scopes
- Audit and compliance - Query validation history and audit trail

