Architecture
Midaz was designed to work in a secure structure. To create secure code and architecture, the concepts of security by design and threat modeling were used from the start and are still applied to every new feature.
- Security by design: Security controls are embedded throughout the lifecycle — from design to deployment — following OWASP guidelines such as the OWASP Top 10 and OWASP Application Security Verification Standard (ASVS) standards.
- Threat Modeling: Structured process used to identify, assess, and mitigate potential security risks in a system before they can be exploited. The methodology used in Midaz is called STRIDE where the threats are categorized in 6 types:
- Spoofing (e.g., fake authentication in a banking API).
- Tampering (e.g., altering transaction data mid-request).
- Repudiation (e.g., lack of audit logs for transactions).
- Information Disclosure (e.g., leaking sensitive data via API responses).
- Denial of Service (e.g., overwhelming the API with fake requests).
- Elevation of Privilege (e.g., exploiting a bug to gain admin access).
Shared responsibility model
Security is a shared responsibility between Lerian and the customer. The exact split depends on your deployment model.
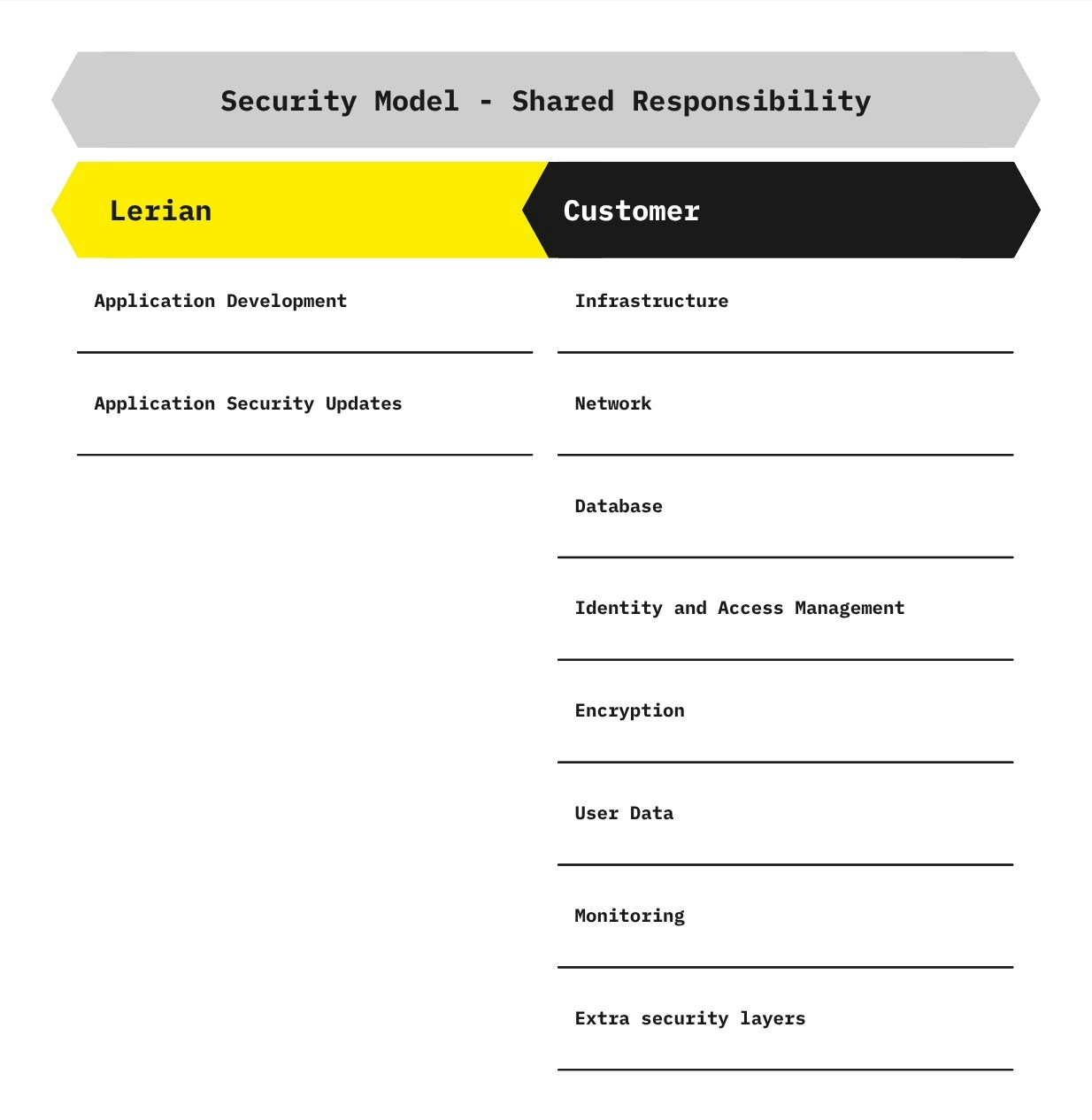
In the BYOC model
In BYOC (Bring Your Own Cloud), you deploy Lerian in your own infrastructure. Lerian secures the application layer. You secure the environment. What Lerian secures:- Building secure-by-design services.
- Proactively addressing vulnerabilities.
- Releasing security updates, including dependency upgrades, security patches, and ongoing improvements.
- Infrastructure: Harden OS and container images, manage patches, and apply secure configurations on the hosting platform.
- Network: Implement segmentation, firewalls, and IDS/IPS systems. Adopt Zero Trust principles to protect internal and external communication.
- Database: Set up backups, audit logging, and follow security best practices for data storage.
- Identity & Access Management: Control access to the environment and leverage Midaz’s RBAC features to enforce least-privilege policies within the platform.
- Encryption: Encrypt sensitive data at rest and in transit. Consider tokenization or anonymization where appropriate.
- User Data: All user data stored or processed via Midaz remains fully under the customer’s control and responsibility.
- Monitoring: Establish monitoring tools capable of detecting unusual access patterns or suspicious behavior.
- Additional Security Layers: Reinforce defenses with Web Application Firewalls (WAF), anti-DDoS mechanisms, and bot mitigation tools.
In the SaaS model
In SaaS, Lerian manages the full infrastructure. The security responsibility shifts — Lerian takes on significantly more. What Lerian secures:- Everything in the BYOC application layer, plus:
- Cloud infrastructure, networking, and compute environment.
- Database provisioning, encryption at rest, and automated backups.
- OS and container patching.
- Monitoring, alerting, and incident response.
- High availability and disaster recovery.
- Business-level access control: Manage users, roles, and permissions within the platform.
- API integration security: Secure the communication between your systems and the Lerian APIs.
- User Data governance: Define and enforce data handling policies that meet your regulatory obligations.
- Compliance: Ensure your use of the platform aligns with your institution’s regulatory requirements.
Identity and Access Management
Midaz is designed to support OAuth 2.0 by default, giving customers flexibility to choose how they manage identity and access. You have two options:
- Use your own external IAM (Identity and Access Management) solution.
- Use Lerian’s native Access Manager Plugin — ideal for customers without an existing IAM system or those looking for a fully integrated experience.
Option 1: External IAM
If you prefer to integrate your own IAM provider, you must ensure it follows modern security practices. To keep Midaz secure, we strongly recommend:- Using proven protocols such as OAuth 2.0 and OpenID Connect.
- Requiring Multi-Factor Authentication (MFA).
- Applying strong password hashing algorithms, like bcrypt or argon2.
- Enforcing fine-grained access controls via RBAC, ABAC, or similar models.
- Managing sessions securely, including expiration rules and refresh token policies.
- Protecting endpoints from brute-force and replay attacks.
- Enabling and reviewing access logs regularly.
Option 2: Access Manager Plugin
Our Access Manager Plugin offers a seamless way to manage authentication and authorization inside Midaz. It’s fully integrated and helps streamline deployment by enabling:- User lifecycle management
- Session token handling
- Refresh token rotation
- Application registration and management
Tenant isolation in multi-tenant deployments
When running on Lerian SaaS or BYOC Multi-Tenant, all resources — organizations, ledgers, accounts, transactions — are isolated by tenant at the application layer. Tenant context is established through your JWT access token. The platform’s middleware resolves the tenant on every incoming request using the
tenantId claim embedded in the token. No data from other tenants is ever exposed to your API calls, and your data is never accessible to other tenants.
This isolation operates independently of the organization hierarchy. Even if two tenants create similar organization structures, their data is completely separate — each tenant operates on its own database.
Data protection
Midaz enforces double-entry principles by design—every transaction must have balanced debits and credits. If an entry fails this validation, it’s automatically rejected. This not only ensures ledger integrity but also protects the system against race condition vulnerabilities and posting discrepancies.
Built-in safeguards
To maintain consistency and prevent logic errors, Midaz applies strict validation across all transaction flows:- Negative balances are blocked unless explicitly permitted.
- Account status is verified before allowing any operation.
- Assets must be registered and valid at the time of posting.
Compliance with LGPD and GDPR
While Midaz handles transactional validation and secure communication (via TLS 1.2 and 1.3), customers are responsible for protecting personally identifiable information (PII). To stay compliant with LGPD, GDPR, and similar data protection laws, we recommend:- Applying encryption for sensitive data, both at rest and in transit.
- Using tokenization or anonymization when appropriate.
- Storing and managing customer data under clearly defined security policies.
Responsible disclosure policy
We believe that transparency builds trust. That’s why all known security improvements and fixes are shared openly in our GitHub Discussions. This allows the community to stay informed about ongoing security patches and enhancements. If you identify a security vulnerability in Midaz, please report it directly to our team before making it public. We fully support responsible disclosure and are committed to investigating and resolving issues quickly and thoroughly.
Please refrain from publicly disclosing any findings until we’ve had a chance to review and address them.
Report
Email us at security@lerian.studio.

